LinkDaddy Universal Cloud Storage Press Release: Announcing New Features
LinkDaddy Universal Cloud Storage Press Release: Announcing New Features
Blog Article
Secure Your Data: Best Practices for Implementing Universal Cloud Storage Services
The benefit of global cloud storage space comes with the duty of guarding delicate information against prospective cyber hazards. By discovering crucial approaches such as data file encryption, accessibility control, back-ups, multi-factor authentication, and continual monitoring, you can establish a solid protection against unauthorized access and data violations.
Information File Encryption Steps
To boost the security of data stored in global cloud storage solutions, robust information encryption steps need to be carried out. Data file encryption is an important element in securing sensitive details from unauthorized gain access to or violations. By transforming information right into a coded layout that can only be understood with the appropriate decryption key, security makes sure that even if data is intercepted, it continues to be muddled and protected.
Applying strong security formulas, such as Advanced Security Requirement (AES) with an enough crucial length, includes a layer of defense against possible cyber risks. Additionally, making use of secure essential monitoring methods, including routine crucial rotation and safe and secure crucial storage, is important to maintaining the integrity of the security process.
Additionally, organizations ought to consider end-to-end file encryption solutions that encrypt information both in transportation and at rest within the cloud storage atmosphere. This detailed approach helps mitigate risks linked with information direct exposure during transmission or while being saved on servers. Overall, prioritizing data file encryption steps is paramount in fortifying the protection stance of universal cloud storage services.
Gain Access To Control Policies

Access control plans should be based on the concept of the very least opportunity, providing users the minimum level of access required to do their job functions properly. This assists lessen the danger of unapproved accessibility and potential information breaches. Furthermore, multifactor authentication ought to be utilized to include an added layer of safety, needing customers to supply multiple forms of verification before accessing delicate data.
Regular Information Backups
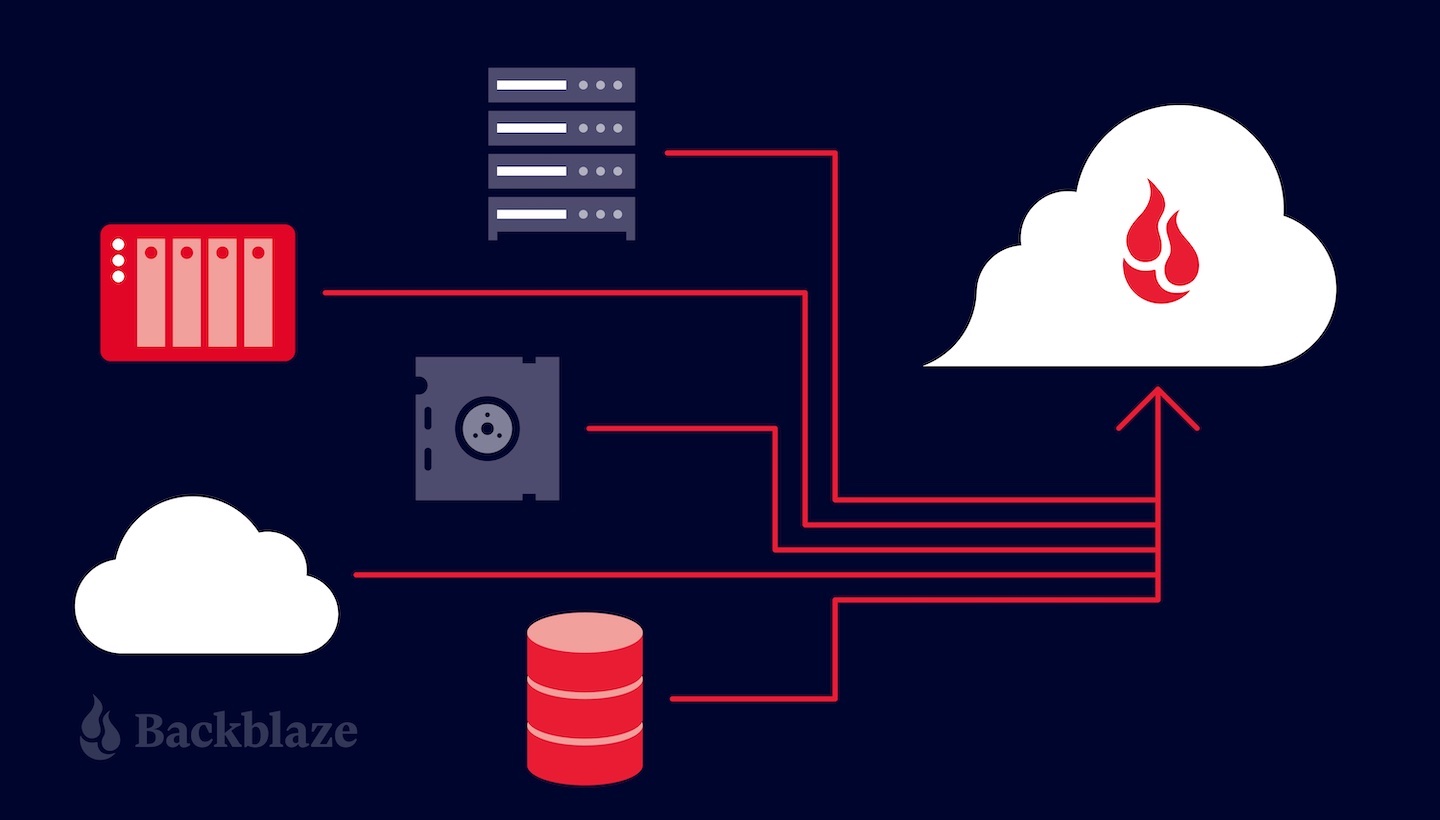
Executing a robust system for regular data back-ups is necessary for guaranteeing the resilience and recoverability of information saved in global cloud storage services. Normal back-ups work as an essential security internet against information loss as a result of accidental deletion, corruption, cyber-attacks, or system failings. By developing a regular back-up routine, organizations can lessen the threat of disastrous data loss and maintain business connection in the face of unexpected events.
To effectively execute regular data backups, companies must follow ideal practices such as automating backup procedures to ensure consistency and reliability - linkdaddy universal cloud storage press release. It is vital to verify the honesty of back-ups regularly to guarantee that information can be successfully recovered when needed. In addition, storing backups in geographically varied places or utilizing cloud duplication services can further improve information strength and reduce risks connected with localized cases
Ultimately, a positive technique to normal information backups not just safeguards versus data loss but likewise infuses self-confidence in the integrity and accessibility of essential details stored in global cloud storage space solutions.
Multi-Factor Verification
Enhancing safety procedures in cloud storage space services, multi-factor verification gives an extra layer of defense against unapproved accessibility. This technique Home Page calls for users to give 2 or more types of verification before gaining entrance, dramatically reducing the risk of data breaches. By integrating something the user understands (like a password), with something they have (such as a mobile tool for receiving a verification code), or something they are (like biometric information), multi-factor verification enhances safety past just making use of passwords.
This significantly decreases the likelihood of unapproved access and enhances general data security steps. As cyber dangers continue to progress, integrating multi-factor verification is a necessary practice for companies looking to safeguard their data properly in the cloud.
Continual Safety And Security Monitoring
In the realm of guarding sensitive info in universal cloud storage space services, a critical element that complements multi-factor verification is continual protection monitoring. Continual security tracking includes the recurring monitoring and evaluation of a system's safety procedures to identify and reply to any type of possible risks or vulnerabilities without delay. By carrying out continual safety and security monitoring protocols, companies can proactively identify suspicious tasks, unauthorized accessibility attempts, or unusual patterns that might show a protection violation. This real-time tracking allows speedy action to be taken to alleviate threats and safeguard valuable data kept in the cloud. Automated alerts and notices can alert safety and security teams to any type of abnormalities, permitting for prompt examination and removal. Continual safety surveillance helps make certain compliance with regulatory needs by giving a thorough document of protection occasions and actions taken. By integrating this technique right into their cloud storage methods, services can enhance their general protection stance and strengthen their defenses versus progressing cyber dangers.
Verdict

Report this page